A few days ago I got a new computer at work. I took it home to install it, but to finish the installation and log on with my domain account I needed access to the corporate network.
I had to find a solution to finalize the installation without going back to the office. Luckily we have Direct Access configured at my company, and all I need to connect is a domain joined computer. A perfect opportunity to use the Offline Domain Join feature.
For this to work we need some prerequisites in place:
- A Windows Server 2012 or newer Direct Access server
- A domain controller with at least Windows Server 2008 R2
- At least Windows 8 on the client computer
Note: Offline Domain Join works in Windows 7 as well, but these are the minimum requirements to use it in conjunction with Direct Access
This process is performed in two steps: First we have to provision the computer in Active Directory. We create a computer account, and store metadata about the computer in a file. The metadata file is then used on the computer to finish the process.
The information we have to provide during the provisioning is:
- The name of the domain that we want to join the new computer to
- The name of the computer
- Where to save the metadata file
- The Direct Access Group Policy, to get all settings to connect using Direct Access
- We also need to issue a computer certificate for Direct Access, so we have to specify what Certificate Template to use.
Let’s use Djoin.exe to provision the new computer. This command must run on a machine that is already a member of the domain, and you need rights to add workstations to the domain:
Djoin.exe /provision /domain corp.tailspintoys.com /machine PC5441 /savefile c:\OfflineDomainJoin.txt /policynames "DirectAccess Client Settings" /policypaths "\\corp.tailspintoys.com\SYSVOL\corp.tailspintoys.com\Policies\{GUID}\Machine\Registry.pol" /certtemplate Machine
Now, I copy OfflineDomainJoin.txt to the new computer and run Djoin.exe again to insert the metadata into the computer. Please be aware that this file contains sensitive information and should not be sent unencrypted.
Djoin.exe /requestODJ /loadfile C:\OfflineDomainJoin.txt /windowspath %systemroot% /localos
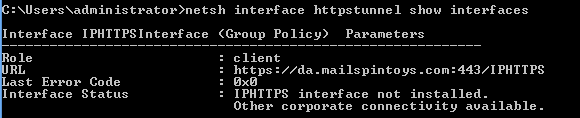
Finally, a restart is required. After the restart I’m connected with Direct Access and it is possible to log on with my domain credentials.
/ Andreas