Disclaimer
This blog post was written for an older version of the Azure AD Connect Synchronization Service. For information regarding the current version please look at the documentation from Microsoft.
Sometimes you need changes in your on-premises Active Directory to sync to Office 365 as soon as possible. You might, for example, have a new employee at your doorstep one morning, and you quickly have to create an account for him. Normally a sync is only done every three hours. With these commands your data is synced immediately.
Depending on your version of DirSync/AADSync the commands are a bit different:
DirSync prior to version 6862.0000
To start a manual sync you launch the DirSyncConfigShell Console File, located at C:\Program Files\Windows Azure Active Directory Sync.
A sync is triggered by the command
Start-OnlineCoexistenceSync
You can also trigger a full sync by using the -FullSync parameter.
If you are using DirSync with Password Sync you can also run a full password sync with the following lines of PowerShell code:
Set-FullPasswordSync
Restart-Service FIMSynchronizationService -Force
The DirSync result can be viewed in the FIM Client, but to see the result of Password Sync you need to look at the Event Viewer in Windows.
DirSync version 6862.0000 and later
Starting with DirSync version 6862.0000 released on June 5 2014 there is no longer a DirSyncConfigShell Console file in the Program Files folder. Instead you just start a normal PowerShell window and run Import-Module DirSync. After that the Start-OnlineCoexistenceSync cmdlet is available.
Forcing a Password Sync uses the same lines of PowerShell code as the previous versions:
Set-FullPasswordSync
Restart-Service FIMSynchronizationService -Force
Azure Active Directory Synchronization Services (AAD Sync)
A Directory Synchronization is triggered by running an exe file:
C:\Program Files\Microsoft Azure AD Sync\Bin\DirectorySyncClientCmd.exe

DirectorySyncClientCmd.exe accept two parameters, initial and delta. Running DirectorySyncClientCmd.exe initial initiates to a FullSync, and running DirectorySyncClientCmd.exe delta (or without any parameters) initiates an incremental sync.
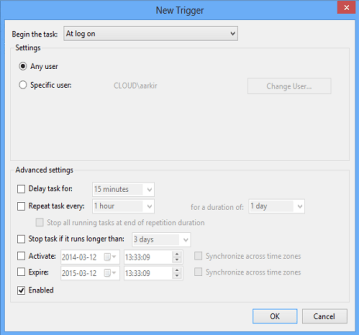
The delta synchronization is triggered every 3 hours, and it can also be started manually by running the Scheduled Task “Azure AD Sync Scheduler” in the Task Scheduler.
To force a Password Sync the following lines of PowerShell code is needed. Modify the first two lines to match your environment.
$adConnector = 'ad.contoso.com'
$aadConnector = 'contoso.onmicrosoft.com - AAD'
Import-Module ADSync
$c = Get-ADSyncConnector -Name $adConnector
$p = New-Object Microsoft.IdentityManagement.PowerShell.ObjectModel.ConfigurationParameter 'Microsoft.Synchronize.ForceFullPasswordSync', String, ConnectorGlobal, $null, $null, $null
$p.Value = 1
$c.GlobalParameters.Remove($p.Name)
$c.GlobalParameters.Add($p)
$c = Add-ADSyncConnector -Connector $c
Set-ADSyncAADPasswordSyncConfiguration -SourceConnector $adConnector -TargetConnector $aadConnector -Enable $false
Set-ADSyncAADPasswordSyncConfiguration -SourceConnector $adConnector -TargetConnector $aadConnector -Enable $true
/ Andreas