Yesterday was a very nervous day for me and the F5 button went warm pretty much the entire day. New quarter means new possibilities to get a Most Valueable Professional Award (MVP) from Microsoft. 16:26 did the email I was hoping for arrive – that I have got an MVP award for my contributions in the Office 365 community!  Thanks for all the support – I am looking forward continuing this journey and will do what I can to keep up with our contributions here and on other platforms together with my fellow MVP’s. /Johan
Thanks for all the support – I am looking forward continuing this journey and will do what I can to keep up with our contributions here and on other platforms together with my fellow MVP’s. /Johan
Author Archives: Johan Dahlbom
Azure AD Sync – Configure attribute based filtering using PowerShell
Most often when synchronizing your directories to AAD, you don’t want all your users to get synchronized. One of the most common methods of filtering out who should get synced and not is by using attributes.
Since AADSync arrived the process of doing this has changed a bit. In this post I will go through how to configure the filtering with PowerShell. Read here about the other methods for filtering objects in AADSync.
In this particular example I will filter out users by the following criteria:
- UserPrincipalName DOES NOT END with @365lab.net
I have created a PowerShell function to make the creation a bit easier to configure the filtering. If not specifying a domain with the -DomainName parameter, it will create the rule for all your domains connected to AADSync (if you have more than one). To create a filtering configuration as in my example, just run the cmdlet as below.
New-JDAADSyncFilteringRule -Name "In from AD - User NoSync Filter" `
-Attribute "userPrincipalName" `
-Value "@365lab.net" `
-Operator NOTENDSWITH `
-Precedence 50

Please note that the filter is not quite as forgiving as most things usually are nowdays when it comes to case-sensitivity.
New-JDAADSyncFilteringRule
function New-JDAADSyncFilteringRule {
<#
.SYNOPSIS
The function will create AADSync filtering rules based on attributes and conditions
.EXAMPLE
New-JDAADSyncFilteringRule "Inbound from AD" -Attribute "userPrincipalName" -Value "@365labf.net" -Operator ENDSWITH -Precedence 50
.NOTES
File Name: New-JDAADSyncFilteringRule
Author : Johan Dahlbom, johan[at]dahlbom.eu
Blog : 365lab.net
The script are provided “AS IS” with no guarantees, no warranties, and they confer no rights.
Requires PowerShell Version 3.0!
#>
[CmdletBinding(SupportsShouldProcess=$true)]
param(
[Parameter(Mandatory=$true)]
[String]
$Name,
[ValidateScript({Get-ADSyncConnector -Name $_})]
[string]
$DomainName,
[Parameter(Mandatory=$true)]
[String]
$Attribute,
[Parameter(Mandatory=$true)]
[String]
$Value,
[Parameter(Mandatory=$true)]
[ValidateSet("EQUAL","NOTEQUAL","NOTENDSWITH","ENDSWITH","CONTAINS","NOTCONTAINS")]
$Operator,
[Parameter(Mandatory=$true)]
[int]
$Precedence
)
#Import ADSync Module
Import-Module ADSync
#Check if connector/domain name has been provided
if ($DomainName) {
$ADConnectors = Get-ADSyncConnector -Name $DomainName
} else {
$ADConnectors = Get-ADSyncConnector | Where-Object {$_.Type -eq "AD"}
}
foreach ($ADConnector in $ADConnectors) {
try {
#Create the Scope Filter Object
$Scopefilter = New-Object Microsoft.IdentityManagement.PowerShell.ObjectModel.ScopeCondition
$Scopefilter.Attribute = $Attribute
$Scopefilter.ComparisonValue = $Value
$Scopefilter.ComparisonOperator = $Operator
#Create the Attribute Flow
$AttrFlowMappings = New-Object Microsoft.IdentityManagement.PowerShell.ObjectModel.AttributeFlowMapping
$AttrFlowMappings.Source = "True"
$AttrFlowMappings.Destination = "cloudFiltered"
$AttrFlowMappings.FlowType = "constant"
$AttrFlowMappings.ExecuteOnce = $False
$AttrFlowMappings.ValueMergeType = "Update"
#Add the Scope Filter to a Scope Group
$ScopeFilterGroup = New-Object Microsoft.IdentityManagement.PowerShell.ObjectModel.ScopeConditionGroup
$ScopeFilterGroup.ScopeConditionList.Add($Scopefilter)
$SyncRuleHt = @{
Connector = $ADConnector.Identifier.Guid
Name = $Name
SourceObjectType = "user"
TargetObjectType = "person"
Direction = "inbound"
AttributeFlowMappings = $AttrFlowMappings
LinkType = "Join"
Precedence = $Precedence
ScopeFilter = $ScopeFilterGroup
}
Add-ADSyncRule @SyncRuleHt | Out-Null
Write-Output "Added the Syncrule $Name ($Precedence) for the attribute $Attribute with the condition $Operator $Value"
} catch {
Write-Warning "$_"
}
}
}
RESULTS
Using the SyncRulesEditor.exe (or the cmdlet Get-ADSyncRule) in the folder where you have installed AADSync (most commonly C:\Program Files\Microsoft Azure AD Sync\UIShell\) and verify that your settings successfully has been saved/configured.
As always, if you have suggestions for improvements of changes in the scripts or posts, let us know! 🙂
Enjoy!
/Johan
Quick Tip: Azure AD Premium features not showing up in the portal
Thought I should share a “problem” that quite a few people have asked me about regarding Azure AD Premium.
THE ISSUE
You sign up up for a trial, or assign a SKU (for example EMS) where Active Directory Premium is included to your tenant. For some reason, no AADP features are showing up in the configure pane when you access your Azure AD as Admin.
SOLUTION
As of now, in order to be able to manage Azure AD Premium, you need to have licenses assigned for each Admin.

After assigning Azure AD Premium Licenses to the Admin account, you will now see all the AADP-features, including Sign in branding and password reset under the configure pane, just as below.

Hope this helps you if running in to this rather simple issue! 🙂
/Johan
Office 365: Deploying your SSO Identity Infrastructure in Microsoft Azure (Using Azure AD Connect) – Part 3
This is the last part of 3 in the series where we go through how to create a highly available SSO infrastructure for Office 365 in Microsoft Azure. In this part we will finish off the configuration and put all the pieces together. To make it a bit more interesting, I’ve also decided to try out the Preview of Azure AD Connect to configure the AADSync, ADFS and WAP servers.
Part 1 of the series can be found here.
Part 2 of the series can be found here.
PROMOTING THE DOMAIN CONTROLLER
If you haven’t already promoted your DC in Azure, the following example snippet will promote the domain controller to your existing domain using the the account you’re logged on with. Note that the Database/Log/Sysvol paths has been changed to the additional disk that was added to the DC. We do this since we need to use a separate volume that is not using host caching for the AD databases in Azure.The server will also automatically reboot after the promotion has been done.
Import-Module ADDSDeployment
$DCPromotionSettings = @{
NoGlobalCatalog = $false
CreateDnsDelegation = $false
CriticalReplicationOnly = $false
DatabasePath = "F:\Windows\NTDS"
LogPath = "F:\Windows\NTDS"
SysvolPath = "F:\Windows\SYSVOL"
DomainName = "365lab.internal"
InstallDns = $true
NoRebootOnCompletion = $false
SiteName = "Azure-IAAS-Dublin"
Force = $true
SafeModeAdministratorPassword = (ConvertTo-SecureString -String 'YourStrongDSRMPassword!' -AsPlainText -Force)
}
Install-ADDSDomainController @DCPromotionSettings
AZURE AD CONNECT?
Instead of using pure PowerShell to configure the servers, I’ve chosen to use the new Azure AD Connect Preview, a one stop shopping-wizard for setup and configuring AADSync, ADFS, WAP against Azure AD. Sounds very promising right?
GETTING THROUGH THE WIZARD
1. Download and install(AzureADConnect.msi) the tool from here. In my case I am running the wizard on the AZURE-AADSYNC1 server.
2. Go through the Prerequisite and Azure tenant wizard as below. Your Azure AD Credentials should of course be a service Account with Global administrator permissions.


3. Since we want to deploy ADFS and WAP during the installation, we click customize to be able to do that.

4. Single sign on it is! In this example we’ll use the federation service name of sts.adfs.guru.

5. Set up connections to your AD forest(s). Note that the credentials used here should be a proper configured service account. Check out this script for a good way to configure delegation on the service account.


6. In my case I’ll have both an Exchange Hybrid deployment and Password Write back through AADP enabled.

7. Since I have only have one forest/domain, I’m just using the default settings for the next two steps.


8. Import the .pfx file for your service. In my case I have a certificate with the CN sts.adfs.guru that will be imported to all ADFS and WAP machines. If you want to set up this in a lab environment, you can use startssl.com (gives you 1 year free single name certificates trusted by most browsers).

9. Now point out your ADFS and WAP servers, in my case I have two of each (as deployed in the last post). Note that you will not be able to add the servers to the wizard unless they have PS Remoting enabled. This can be enabled by running the PowerShell command ‘Enable-PSRemoting -Force’ on each machine (or put it in the deployment script :))

The server with only lower case letters will be the primary ADFS server in the farm.

It gives me a warning regarding the WAP servers since I’ve pre-deployed the WAP role.
10. Now specificy an account with Local Admin credentials on the primary ADFS server, in order to create a trust between the WAP servers and the federation servers.

11. Choose which service Account that should be used for the ADFS farm. I do recommend using Group Managed Service accounts if possible (requires minimum 2012 DC’s). In the GMSA case, the wizard will actually create a KDS Root key in your domain if you haven’t one since before. Note that this is also done with WinRM through the Domain Controller, so make sure you have that enabled there as well.

12. Choose the domain you want to use for the Federated setup. As it seems right now with this preview, you can only create federation for one domain.

13. Review your configuration. If don’t want to start off by synchronize your entire directory, uncheck “Start the synchronization..” and look in to the following site on how to filter your synchronization scope. Fire off the installation by clicking Install.

14. Installation complete! PUH! If you run in to any errors during the installation, or cancel the installation, you’ll be able to continue from where you left.

As seen above, you’ll also have the option of verifying your ADFS service DNS records.
In my case, I’ve configured the service name to point to the Azure Internal Load balancer IP (10.255.255.10) internally, and to the WAP Cloud service name externally (365lab-wap1.cloudapp.net), as seen below:

If you don’t want to rely on your VPN Connection for the internal STS, you could publish the internal ADFS farm through the external cloud service name, and create access rules to only allow your external public IP’s.

And my DNS records turned out to be OK according to the wizard! 🙂
AZURE AD CONNECT – VERDICT
In a very simple to understand wizard we’ve done a normally quite complex task as easy as it can possibly be. The end result in this case is an highly available SSO Identity infrastructure with a little help of Azure IAAS. One thing to be aware of though (might be changed later since this is a preview):
SUMMARY
We have now finished configuring with our highly available SSO Identity infrastructure for our Office 365/Azure Active Directory. Not to hard with the help of PowerShell and the new Azure AD Connect Wizard. I will follow this series up with some additional topics with more detailed information regarding how to create firewall rules between our subnets in Azure, and more.
If you have any questions or suggestions, let me know!
/Johan
Office 365: Assign individual parts of licenses based on groups using PowerShell
Important note: The end of an era with licensing scripts is near… and the beginning of a new one with Azure AD Group Based Licensing is here. Group Based Licensing is now in preview and currently requires a paid Azure AD Subscription. Try it out and give Microsoft your feedback on how they can make it even better!
The story continues… After numerous requests regarding handling parts of licenses in my older licensing scripts , I’ve now created an example on how to do this using security groups.
Please note that this is of course not a complete solution, just an example on how to incorporate this in to one of the earlier solutions created.
SCENARIO
In this example, I will have three groups each assigning different parts of an E3 License. One assiging the Full E3, one assigning Exchange Online and one assigning Lync Online + Office 365 ProPlus.
In order to assign them with PowerShell, we need the ServicePlan name of each part we want to assign. Those can be found with the following command for an E3-license:
(Get-MsolAccountSku | Where-Object {$_.SkuPartNumber -eq "ENTERPRISEPACK"}).ServiceStatus

As seen above the names are pretty easy to recognise, if you are unsure which one is which, you will find a good translation table here.
Disabling plans with PowerShell requires you to to select the ones that you want to disable rather than the ones you want to enable, just like in the portal. In my example I’m choosing the parts I want to assign per group, which means I’m disabling all other parts than just the ones you want.
See the example below how I’ve configured my $Licenses hashtable for my scenario:
$Licenses = @{
'E3-ExchangeOnline' = @{
LicenseSKU = 'tenant:ENTERPRISEPACK'
EnabledPlans = 'EXCHANGE_S_ENTERPRISE'
Group = 'E3-ExchangeOnline-Users'
}
'E3-LyncO365ProPlus' = @{
LicenseSKU = 'tenant:ENTERPRISEPACK'
EnabledPlans = 'MCOSTANDARD','OFFICESUBSCRIPTION'
Group = 'E3-LyncO365ProPlus-Users'
}
'E3' = @{
LicenseSKU = 'tenant:ENTERPRISEPACK'
Group = 'E3-Users'
}
}
RUNNING THE SCRIPT
After editing the $Licenses hashtable, $UsageLocation and tenant credentials, you’re ready to run the script as in the screenshot below.


A user that have been assigned licenses with the E3-LyncO365ProPlus-Users group in the example
LicenseO365Users.ps1
&amp;lt;# .SYNOPSIS Script that assigns Office 365 licenses based on Group membership in AAD. .NOTES Author: Johan Dahlbom Blog: 365lab.net Email: johan[at]dahlbom.eu The script are provided “AS IS” with no guarantees, no warranties, and they confer no rights. Requires PowerShell Version 3.0! #&amp;gt;
#Import Required PowerShell Modules
Import-Module MSOnline
#Office 365 Admin Credentials
$CloudUsername = 'admin@tenant.onmicrosoft.com'
$CloudPassword = ConvertTo-SecureString 'password' -AsPlainText -Force
$CloudCred = New-Object System.Management.Automation.PSCredential $CloudUsername, $CloudPassword
#Connect to Office 365
Connect-MsolService -Credential $CloudCred
$UsageLocation = 'SE'
$Licenses = @{
'E3-ExchangeOnline' = @{
LicenseSKU = 'tenant:ENTERPRISEPACK'
EnabledPlans = 'EXCHANGE_S_ENTERPRISE'
Group = 'E3-ExchangeOnline-Users'
}
'E3-LyncO365ProPlus' = @{
LicenseSKU = 'tenant:ENTERPRISEPACK'
EnabledPlans = 'MCOSTANDARD','OFFICESUBSCRIPTION'
Group = 'E3-LyncO365ProPlus-Users'
}
'E3' = @{
LicenseSKU = 'tenant:ENTERPRISEPACK'
Group = 'E3-Users'
}
}
foreach ($license in $Licenses.Keys) {
$GroupName = $Licenses[$license].Group
$GroupID = (Get-MsolGroup -All | Where-Object {$_.DisplayName -eq $GroupName}).ObjectId
$AccountSKU = Get-MsolAccountSku | Where-Object {$_.AccountSKUID -eq $Licenses[$license].LicenseSKU}
Write-Output "Checking for unlicensed $license users in group $GroupName"
#region Disable non specific plans
$EnabledPlans = $Licenses[$license].EnabledPlans
if ($EnabledPlans) {
$LicenseOptionHt = @{
AccountSkuId = $AccountSKU.AccountSkuId
DisabledPlans = (Compare-Object -ReferenceObject $AccountSKU.ServiceStatus.ServicePlan.ServiceName -DifferenceObject $EnabledPlans).InputObject
}
$LicenseOptions = New-MsolLicenseOptions @LicenseOptionHt
}
#endregion Disable non specific plans
#Get all unlicensed group members - needs to be changed if a user should be able to have more than one license
$GroupMembers = (Get-MsolGroupMember -GroupObjectId $GroupID -All | Where-Object {$_.IsLicensed -eq $false}).EmailAddress
#Warn if not enough licenses are available
if ($AccountSKU.ActiveUnits - $AccountSKU.consumedunits -lt $GroupMembers.Count) {
Write-Warning 'Not enough licenses for all users, please remove user licenses or buy more licenses'
}
foreach ($User in $GroupMembers) {
try {
#Set UsageLocation
Set-MsolUser -UserPrincipalName $User -UsageLocation $UsageLocation -ErrorAction Stop -WarningAction Stop
$LicenseConfig = @{
UserPrincipalName = $User
AddLicenses = $AccountSKU.AccountSkuId
}
if ($EnabledPlans) {
$LicenseConfig['LicenseOptions'] = $LicenseOptions
}
Set-MsolUserLicense @LicenseConfig -ErrorAction Stop -WarningAction Stop
Write-Output "SUCCESS: licensed $User with $license"
} catch {
Write-Warning "Error when licensing $User`r`n$_"
}
}
}
Let me know if you have any questions or feedback!
/Johan
Automating the creation of an OU structure based on a template
Discussing OU structures in an Active Directory can easily get into a religious matter. 🙂
Anyhow, the reality is that different organizations have different needs. Therefore, you sometimes end up with more or less complex OU structures. In order to make the creation of the ‘more complex structures’ as the one in the screenshot below easier, I’ve created a small function that lets you copy the structure from a template or from an existing, already properly configured site/structure.

function Copy-JDOrganizationalUnit {
<#
.SYNOPSIS
The script copies an OU structure from one OU to another. The destination OU must already be created.
.EXAMPLE
Copy-JDOrganizationalUnit -SourcePath "OU=HAB,OU=SE,OU=Sites,DC=lucernepublishing,DC=local" -DestinationPath "OU=HEL,OU=FI,OU=Sites,DC=lucernepublishing,DC=local" -Verbose
.PARAMETER SourceOU
Plain name of the source OU to copy the structure from.
.PARAMETER DestinationOU
Plain name of the destination OU to replicate the structure to.
.PARAMETER ProtectOU
Sets the flag ProtectOUFromAccidentialDeletion
.NOTES
File Name: Copy-JDOrganizationalUnit
Author : Johan Dahlbom, johan[at]dahlbom.eu
Blog : 365lab.net
The script are provided “AS IS” with no guarantees, no warranties, and they confer no rights.
#>
[CmdletBinding(SupportsShouldProcess=$true,HelpUri = 'http://www.365lab.net/')]
param (
[Parameter(Mandatory=$true,ValueFromPipeline=$true,ValueFromPipelineByPropertyName=$true)]
[ValidateScript({Get-ADOrganizationalUnit -Identity $_})]
[string]$SourcePath,
[Parameter(Mandatory=$true,ValueFromPipeline=$true,ValueFromPipelineByPropertyName=$true)]
[ValidateScript({Get-ADOrganizationalUnit -Identity $_})]
[string]$DestinationPath,
[switch]$ProtectOU
)
Write-Verbose "Copying structure from $SourcePath to $DestinationPath..."
Get-ADOrganizationalUnit -SearchBase $SourcePath -Filter {Distinguishedname -ne $SourcePath} -Properties canonicalname| Select-Object DistinguishedName,canonicalname,Name | Sort-Object -Property CanonicalName | ForEach-Object {
try {
$NewOU = @{
Path = $_.DistinguishedName.replace("OU=$($Name),",'').Replace("$SourcePath","$DestinationPath")
Name = $_.Name
ProtectedFromAccidentalDeletion = $ProtectOU
}
New-ADOrganizationalUnit @NewOU -ErrorAction Stop
Write-Verbose "Created OU OU=$Name,$DestPath"
} catch {
Write-Warning "Error with creating OU=$Name,$DestPath`r`n$_"
}
}
}
Running the example as below, will copy the entire structure from OU=JKG to OU=BRU. It will not overwrite any existing OU’s.
$OUs = @{
SourcePath = 'OU=JKG,OU=SE,OU=Sites,DC=365lab,DC=internal'
DestinationPath = 'OU=BRU,OU=BE,OU=Sites,DC=365lab,DC=internal'
}
Copy-JDOrganizationalUnit @OUs -Verbose -ProtectOU
As you can see above, the entire structure has now been copied according to the Source OU. Let me know if you have feedback or suggestions on improvements!
/Johan
Change DNS settings on multiple servers
A common change that is required to be done when doing major infrastructure upgrades is changing dns server settings on clients and servers. Something that I often see is that the changes on the servers are handled manually by logging on with RDP, changing DNS and logging of. Therefore I wanted to share a basic script that does this job for you, for all or a set of servers in Active Directory through WMI. It can of course be customized indefinitely according to your DNS topology and site structure.
By default it will target all servers that are not domain controllers, respond to ping and WMI.
If you have a simple environment with example only two or three DNS servers it’s just to change the $NewDNS array to your specific DNS servers and run the script.
ChangeDNSServers.ps1
Import-Module ActiveDirectory
#New DNS Servers in order
$NewDNS = @("10.255.255.4","10.255.255.5")
$NewDNS | ForEach-Object -Begin { Write-Output "The following DNS servers in order will be set on the machines:" ; $index = 1} -Process { Write-Output "#$($index): $_" ; $index++ }
#Get all servers in active directory (excluding domain controllers)
$ServersToChange = (Get-ADComputer -Filter {operatingsystem -like "*Server*" -and enabled -eq $true -and primarygroupid -ne '516'}).Name
#Loop through all servers and change to the new DNS servers
foreach ($Server in $ServersToChange) {
if (Test-Connection -ComputerName $Server -Count 1 -Quiet -ErrorAction Ignore -WarningAction Ignore) {
try {
$wmi = Get-WmiObject -Class win32_networkadapterconfiguration -Filter "ipenabled = 'true'" -ComputerName $Server
$wmi.SetDNSServerSearchOrder($NewDNS) | Out-Null
Write-Output "SUCCESS: Changed DNS on $Server"
} catch {
Write-Warning "Error changing DNS on $Server"
}
} else {
Write-Warning "Error contacting $Server`r`nDoes it respond to ping/wmi?"
}
}

WHAT COULD POSSIBLY GO WRONG?
Changing DNS server settings on a machine is not something that you usually think could break anything. In 11/10 times there are no issues at all. But the 12th time you do it, you might get in trouble. So, if you have Windows Server 2008/2008 R2 machines in your environment, please read KB2520155 make sure to apply proper countermeasure prior to changing DNS servers on those.
/Johan
Office 365: Deploying your SSO Identity Infrastructure in Microsoft Azure – Part 2
This is part 2 of 3 in a series where we go through how to create a highly available SSO infrastructure for Office 365 in Microsoft Azure. In this part we will deploy all infrastructure components such as virtual machines and load balancers, all with help from PowerShell!
Part 1 of the series can be found here.
Part 3 of the series can be found here.
As mentioned, in order to automate the process of creating the SSO-infrastructure in Azure, I’ve created a PowerShell script/Hydration Kit that does that for you. Based on input from a CSV file, the Machines will not only be provisioned, they will also be configured based on their specific role as follows:
All Machines will
- Join the domain specified in the $DomainName parameter. If you for example would like to exclude the WAP-servers from getting AD-joined, that’s something for a later version of the script.
- Get the Telnet-Client Installed (Important 🙂 ).
- Get an Azure static ip assignment/subnet and InstanceSize based on the input from the CSV file.
- Be placed in the correct cloud service, availability set (if not set to ‘None’) and subnet as specified in the CSV file.
- Get the Operating System specified in the $ImageFamily parameter installed.
Domain Controller
- One 60gb extra DataDisk with HostCaching will be added to the machine (will be initialized and formatted)
- The role AD-Domain-Services will be installed. Note that the Domain Controller will not be promoted automatically by the script.
ADFS Server
- An Azure Internal Load Balancer will be added with the IP Address specified in the CSV file.
- Endpoints for HTTPS will be added to the Load Balancer pointing at the servers.
- The role ADFS-Federation will be installed.
Web Application Proxy
- An external load balanced HTTPS endpoint will be added.
- The role Web-Application-Proxy will be installed.
GETTING STARTED
Assumptions
In order for the script to work properly, you need to have the base infrastructure (AffinityGroups, Virtual Networks/Subnets/DNS) in place prior to running the script. Since the script is automatically joining the VM’s to the domain specified, you need to have connectivity to your local domain as well.
The Default WinRM Endpoint is used to configure the machines, which means you might get issues if your firewall is blocking high ports, such as in the screenshot below.

The Azure PowerShell module do of course need to be installed on the machine you are running the script.
RUNNING THE SCRIPT
1. First, download the script and the csv sample file from here.
2. Edit the csv file according to your needs, make sure that you put the related servers (WAP, ADFS) in the same CloudService, Subnet and Availabilityset etc. For the ADFS servers, you also need to add the Internal Load Balancer IP in the InternalLB column.

3. Run the script. Remember to change the parameters to match your Azure tenant configuration.If you haven’t already added your Account to the session, you will be prompted to do so. You will find screenshots of the steps below. If you lose your Azure session (internet problems etc.) while running, the script can safely be restarted, and will pickup where it stopped after some verification steps.
.\CreateO365AzureEnvironment.ps1 -Verbose -InputFile .\AzureMachines.csv
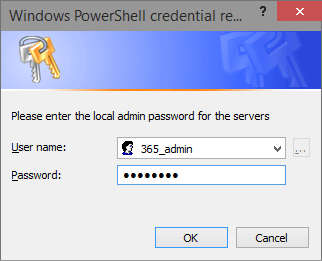
a. Prompted for domain join credentials

b. Prompted to set local admin credentials for the new servers
c. Prompted for Azure tenant credentials

4. Grab some coffee and watch PowerShell do the magic. The entire deployment has taken between 35-45 minutes when I’ve been running it. If you don’t like having the WinRM Endpoint on each exposed to the internet, you need to remove them manually after deployment.

CreateO365AzureEnvironment.ps1
<#
.SYNOPSIS
The scripts creates and configures virtual machines in Microsoft Azure based on an input CSV file.
.EXAMPLE
.\CreateO365AzureEnvironment.ps1 -InputFile '.\AzureMachines.csv' -Verbose
.NOTES
File Name: CreateO365AzureEnvironment.ps1
Author : Johan Dahlbom, johan[at]dahlbom.eu
Blog : 365lab.net
The script are provided “AS IS” with no guarantees, no warranties, and they confer no rights.
Requires PowerShell Version 3.0!
#>
[CmdletBinding(SupportsShouldProcess=$true)]
param (
[Parameter(Mandatory=$false)][string]$AffinityGroup = '365lab-affinitygroup',
[Parameter(Mandatory=$false)][string]$DomainName = '365lab.internal',
[Parameter(Mandatory=$false)][string]$DomainShort = '365lab',
[Parameter(Mandatory=$false)][string]$ImageFamily = 'Windows Server 2012 R2 Datacenter',
[Parameter(Mandatory=$false)][string]$VnetName = '365lab-azure',
[Parameter(Mandatory=$false)][string]$AdminUsername = '365_admin',
[Parameter(Mandatory=$false)][ValidateNotNullOrEmpty()]$DomainJoinCreds = (Get-Credential -Message 'Please enter credentials to join the server to the domain'),
[Parameter(Mandatory=$false)][ValidateNotNullOrEmpty()]$VMCredentials = (Get-Credential -Message 'Please enter the local admin password for the servers' -UserName $AdminUsername),
[Parameter(Mandatory=$false)][ValidateScript({Import-Csv -Path $_})]$InputFile = '.\AzureMachines.csv'
)
#Check that script is running in an elevated command prompt
if (-not([Security.Principal.WindowsPrincipal] [Security.Principal.WindowsIdentity]::GetCurrent()).IsInRole("S-1-5-32-544")) {
Write-Warning "You need to have Administrator rights to run this script!`nPlease re-run this script as an Administrator in an elevated powershell prompt!"
break
}
#region functions
function Connect-Azure {
begin {
try {
Import-Module Azure
} catch {
throw "Azure module not installed"
}
} process {
if (-not(Get-AzureSubscription -ErrorAction Ignore).IsCurrent -eq $true) {
try {
Add-AzureAccount -WarningAction stop -ErrorAction Stop
} catch {
throw "No connection to Azure"
}
}
} end {
$AzureSubscription = Get-AzureSubscription -Default -ErrorAction Ignore
Set-AzureSubscription -SubscriptionId $AzureSubscription.SubscriptionId -CurrentStorageAccountName (Get-AzureStorageAccount -WarningAction Ignore).StorageAccountName
Write-Verbose "Connected to Azure"
}
}
function Configure-JDAzureVM {
[CmdletBinding(SupportsShouldProcess=$true)]
Param(
[Parameter(Mandatory=$true)][ValidateNotNullOrEmpty()][string]$Role,
[Parameter(Mandatory=$false)][ValidateNotNullOrEmpty()]$VMCredentials,
[Parameter(Mandatory=$true)][ValidateNotNullOrEmpty()][string]$VM,
[Parameter(Mandatory=$true)][ValidateNotNullOrEmpty()][string]$CloudService,
[Parameter(Mandatory=$true)][ValidateNotNullOrEmpty()][string]$VMUri,
[Parameter(Mandatory=$false)][ValidateNotNullOrEmpty()][string]$InternalLBIP,
[Parameter(Mandatory=$true)][ValidateNotNullOrEmpty()][string]$Subnet
)
begin {
Write-Verbose "Starting to configure $VM..."
}
process {
#Install mandatory features
$AzureVM = Get-AzureVM -ServiceName $CloudService -Name $VM
#Establish a PS Session to the AzureVM
$SessionOptions = New-PSSessionOption -SkipCACheck -SkipCNCheck
$VMSessionConfig = @{
ConnectionUri = $VMUri
SessionOption = $SessionOptions
Credential = $VMCredentials
}
$VMSession = New-PSSession @VMSessionConfig -ErrorAction Stop
#Install mandatory features
Write-Verbose "Installing mandatory features on $VM"
Invoke-Command -Session $VMSession -ScriptBlock {
#Install the MOST IMPORTANT FEATURE of them all!
Add-WindowsFeature -Name Telnet-Client -IncludeManagementTools -WarningAction Ignore
}
#Install features per role
Write-Verbose "$VM is $Role."
switch ($Role) {
'Domain Controller' {
#Add additional data disk to the domain controller, with host caching disabled
if (-not(Get-AzureDataDisk -VM $AzureVM)) {
Write-Verbose "Adding additional data disk..."
Add-AzureDataDisk -CreateNew -DiskSizeInGB 60 -DiskLabel "ADDB" -HostCaching None -LUN 0 -VM $AzureVM | Update-AzureVM -ErrorAction Stop
}
Write-Verbose "Installing role 'AD-Domain-Services'"
Invoke-Command -Session $VMSession -ScriptBlock {
#Initialize and format additional disks
Get-Disk | Where-Object {$_.PartitionStyle -eq 'raw'} | Initialize-Disk -PartitionStyle MBR -PassThru | New-Partition -AssignDriveLetter -UseMaximumSize |
Format-Volume -FileSystem NTFS -NewFileSystemLabel "ADDB" -Confirm:$false
#Install Role specific features
Add-WindowsFeature -Name AD-Domain-Services -IncludeManagementTools -WarningAction Ignore
}
} 'ADFS Server' {
#Create Internal Load Balancer for the ADFS farm if not already created
if (-not(Get-AzureInternalLoadBalancer -ServiceName $CloudService) -and $InternalLBIP) {
Write-Verbose "Creating/adding $vm to Internal Load Balancer $($AzureVM.AvailabilitySetName) ($InternalLBIP)"
Add-AzureInternalLoadBalancer -ServiceName $CloudService -InternalLoadBalancerName $azurevm.AvailabilitySetName -SubnetName $Subnet -StaticVNetIPAddress $InternalLBIP
}
#Add the server to the Internal Load Balanced set and add 443 as endpoint
if (-not((Get-AzureEndpoint -VM $AzureVM).InternalLoadBalancerName -eq $AzureVM.AvailabilitySetName)) {
Write-Verbose "Adding Internal Load Balanced endpoint on port 443 to $VM"
Add-AzureEndpoint -Name HTTPS -Protocol tcp -LocalPort 443 -PublicPort 443 -LBSetName $AzureVM.AvailabilitySetName -InternalLoadBalancerName $AzureVM.AvailabilitySetName -VM $AzureVM -DefaultProbe | Update-AzureVM -ErrorAction Stop
}
Write-Verbose "Installing role 'ADFS-Federation'"
Invoke-Command -Session $VMSession -ScriptBlock {
#Install Role specific features
Add-WindowsFeature -Name ADFS-Federation -IncludeManagementTools -WarningAction Ignore
}
} 'Web Application Proxy' {
#Add the server to the Cloud Service Load Balanced set and add 443 as endpoint
if (-not((Get-AzureEndpoint -VM $AzureVM).LBSetName -eq $AzureVM.AvailabilitySetName)) {
Write-Verbose "Adding Load Balanced endpoint on port 443 to $CloudService.cloudapp.net"
Add-AzureEndpoint -Name HTTPS -Protocol tcp -LocalPort 443 -PublicPort 443 -LBSetName $AzureVM.AvailabilitySetName -VM $AzureVM -DefaultProbe -LoadBalancerDistribution sourceIP | Update-AzureVM -ErrorAction Stop
}
Write-Verbose "Installing role 'Web-Application-Proxy'"
Invoke-Command -Session $VMSession -ScriptBlock {
#Install Role specific features
Add-WindowsFeature -Name Web-Application-Proxy -IncludeManagementTools -WarningAction Ignore
}
}
}
}
end {
Write-Verbose "Finished configuring $VM"
}
}
function New-JDAzureVM {
[CmdletBinding(SupportsShouldProcess=$true)]
Param(
[Parameter(Mandatory=$true)][ValidateNotNullOrEmpty()][string]$VMName = '',
[Parameter(Mandatory=$true)][ValidateNotNullOrEmpty()][string]$CloudService,
[Parameter(Mandatory=$true)][ValidateNotNullOrEmpty()][string]$IPAddress,
[Parameter(Mandatory=$true)][ValidateNotNullOrEmpty()][string]$Size,
$VMCredentials,
$DomainJoinCreds,
[Parameter(Mandatory=$true)][ValidateNotNullOrEmpty()][string]$SubnetName,
[Parameter(Mandatory=$true)][ValidateNotNullOrEmpty()][string]$OperatingSystem,
[Parameter(Mandatory=$true)][ValidateNotNullOrEmpty()][string]$VnetName,
[Parameter(Mandatory=$true)][ValidateNotNullOrEmpty()][string]$AvailabilitySet,
[Parameter(Mandatory=$true)][ValidateNotNullOrEmpty()][string]$AffinityGroup
)
if (-not(Get-AzureVM -ServiceName $CloudService -Name $VMName -WarningAction Ignore)) {
#region VM Configuration
#Get the latest VM image based on the operating system choice
$ImageName = (Get-AzureVMImage | Where-Object {$_.ImageFamily -eq $OperatingSystem} | Sort-Object -Property PublishedDate -Descending | Select-Object -First 1).ImageName
#Construct VM Configuration
$VMConfigHash = @{
Name = $VMName
InstanceSize = $Size
ImageName = $ImageName
}
if ($AvailabilitySet -ne 'None') {
$VMConfigHash["AvailabilitySetName"] = $AvailabilitySet
}
#VM Provisioning details
$VMProvisionHash = @{
AdminUsername = $VMCredentials.UserName
Password = $VMCredentials.GetNetworkCredential().Password
JoinDomain = $DomainName
DomainUserName = $DomainJoinCreds.UserName.split("\")[1]
DomainPassword = $DomainJoinCreds.GetNetworkCredential().Password
Domain = $DomainShort
}
#Create VM configuration before deploying the new VM
$VMConfig = New-AzureVMConfig @VMConfigHash | Add-AzureProvisioningConfig @VMProvisionHash -WindowsDomain -NoRDPEndpoint |
Set-AzureStaticVNetIP -IPAddress $IPAddress | Set-AzureSubnet -SubnetNames $SubnetName |
Set-AzureVMBGInfoExtension -ReferenceName 'BGInfo'
#endregion VM Configuration
#region Create VM
Write-Verbose "Creating $VMName in the Cloud Service $CloudService"
$AzureVMHash = @{
ServiceName = $CloudService
VMs = $VMConfig
VnetName = $VnetName
AffinityGroup = $AffinityGroup
}
New-AzureVM @AzureVMHash -WaitForBoot -ErrorAction Stop -WarningAction Ignore
#endregion Create VM
} else {
Write-Warning "$VMName do already exist..."
}
}
#endregion functions
#Connect with Azure PowerShell
Connect-Azure
$AzureMachines = Import-Csv -Path $InputFile
Write-Verbose "Starting deployment of machines at: $(Get-date -format u)"
foreach ($Machine in $AzureMachines) {
Write-Verbose "Starting to process $($Machine.Name)"
#Create VM Configuration hashtable based on input from CSV file
$VirtualMachine = @{
VMName = $Machine.Name
CloudService = $Machine.CloudService
IPAddress = $Machine.IP
VMCredentials = $VMCredentials
DomainJoinCreds = $DomainJoinCreds
SubnetName = $Machine.SubnetName
AvailabilitySet = $Machine.AvailabilitySet
AffinityGroup = $AffinityGroup
Size = $Machine.Size
VnetName = $VnetName
OperatingSystem = $ImageFamily
}
try {
#Create virtual machine
New-JDAzureVM @VirtualMachine -ErrorAction Stop
#Wait for machine to get to the state "ReadyRole" before continuing.
while ((Get-AzureVM -ServiceName $Machine.CloudService -Name $Machine.Name).status -ne "ReadyRole") {
Write-Verbose "Waiting for $($Machine.Name) to start..."
Start-Sleep -Seconds 15
}
$VMUri = Get-AzureWinRMUri -ServiceName $machine.CloudService -Name $Machine.Name
#Create VM Role configuration
$VMRoleConfiguration = @{
Role = $Machine.Role
VMUri = $VMUri
VMCredentials = $VMCredentials
VM = $Machine.Name
CloudService = $Machine.CloudService
Subnet = $machine.SubnetName
}
#Add internal load balancer IP to the role configuration
if ($Machine.InternalLB) {
$VMRoleConfiguration["InternalLBIP"] = $Machine.InternalLB
}
#Role specific configuration of the virtual machine
Configure-JDAzureVM @VMRoleConfiguration -ErrorAction Stop
} catch {
Write-Warning $_
}
}
Write-Verbose "Finished deployment of machines at: $(Get-date -format u)"
RESULTS
After some waiting for the provisioning, we now have the infrastructure in place in order to complete the configuration of our SSO infrastructure for Office 365 in Microsoft Azure. In the next part of this series we will put all the pieces together and finish AADSync, ADFS and WAP configuration against Office 365 / Azure Active Directory.

Enjoy, let me know if you have any feedback!
/Johan
Office 365: Deploying your SSO Identity Infrastructure in Microsoft Azure – Part 1
This is part 1 of 3 in a series where we go through how to create a highly available SSO infrastructure for Office 365 in Microsoft Azure.
Part 2 of the series can be found here.
Part 3 of the series can be found here.
Implementing SSO infrastructure with ADFS is something many customers want in order to reduce the amount of logins for their end users. Soon we will even get single sign on in the Outlook client! (YAY 🙂 ) The biggest challenge implementing the infrastructure is that you get dependent on your local server infrastructure and internet connection.
When it’s not possible to make the solution redundant with you own infrastructure, but still need single signon, my recommendation is to deploy the SSO infrastructure in Microsoft Azure.
THE OPTIONS
Microsoft has provided a white paper on the topic that gives you an idea on what options you have and important things to consider. The White paper describes two deployment options implementing the infrastructure in Azure.
- All Office 365 SSO integration components deployed in Azure. This is cloud-only approach; you deploy directory synchronization and AD FS in Azure. This eliminates the need to deploy on-premises servers.
- Some Office 365 SSO integration components deployed in Azure for disaster recovery. This is the mix of on-premises and cloud-deployed components; you deploy directory synchronization and AD FS, primarily on-premises and add redundant components in Azure for disaster recovery.
Option 1 to put the entire Identity Infrastructure in the cloud has been the choice for most of the implementations I’ve been involved in. This gives you a very flexible solution that will provide you a highly available SSO infrastructure, yet putting the infrastructure near the services you are providing.
SETTING IT UP – NETWORK AND STORAGE
In order to set it up in a highly available SSO infrastructure in Azure, the following components/servers must be deployed in Azure. Recommendations on the high-level architecture is also described on http://technet.microsoft.com/en-us/library/dn509538.aspx.
First of all, if you’re setting up your Azure Infrastructure from scratch, you need a virtual network and a storage account in the region that is closest/best for you (in my case, North Europe). See the following tutorials on how to create a virtual network, a storage account and an affinity group.
In my example – the virtual network in Azure is configured as follows:
The network 10.255.255.0/24 is divided into two subnets except for the gateway subnet. One “Internal” subnet and one “Perimeter” subnet in order to filter traffic based on the source/destination IP, that is now possible through Network Security Groups (NSG’s) in Azure. A local network has also been added for on-premises connectivity.
SETTING IT UP – VIRTUAL MACHINES
In my example, I will deploy six(6) virtual Machines with the following roles:
| Name | Role | IP | Size | Cloud Service | Availability Set |
| AZURE-DC1 | Domain Controller | 10.255.255.4 | Small | 365lab-azr01 | |
| AZURE-AADSYNC1 | DirSync/AADSync | 10.255.255.5 | Medium | 365lab-azr01 | |
| AZURE-ADFS01 | ADFS Server | 10.255.255.6 | Small | 365lab-sts | sts-365lab |
| AZURE-ADFS02 | ADFS Server | 10.255.255.7 | Small | 365lab-sts | sts-365lab |
| AZURE-WAP01 | Web Application Proxy | 10.255.255.132 | Small | 365lab-wap | wap-365lab |
| AZURE-WAP02 | Web Application Proxy | 10.255.255.133 | Small | 365lab-wap | wap-365lab |
In this case, I’m choosing to deploy only one domain controller in Azure, and configure that one as the primary dns for the virtual network, and the local network domain controllers as secondary dns servers. Note that the ADFS and WAP servers are placed in separate cloud services/availability sets in order to make them highly available.
You will find a reference regarding machine sizing here. Estimated costs per month for the above setup will with list pricing be around $500 including network traffic and storage. The exact pricing will of course be depend on your Azure agreement and network traffic.
The overall high level design of the setup will be as in the following sketch:

In the next part of the series, we will deploy the virtual Machines with the proper configuration using Azure PowerShell.
Until next time!
/Johan
Exchange Online: Dynamically add mailbox permissions through groups
Managing shared and resource mailbox permissions can be more or less a pain depending on how you do it. Adding users directly as delegates to the shared mailboxes gives you a bit more administrative overhead, but makes it possible to utilize the AutoMapping feature that automatically adds the additional mailboxes to the end users Outlook client. If you instead add mail-enabled security groups to the delegate list, you get less administrative overhead, but not the AutoMapping feature.
Even though this is a really “old” problem, I get questions around it almost every week. Therefore I wanted to share a solution with you that gives you an example on how to solve it still using groups. A script that will use Mail-Enabled Security Groups/Distribution Groups to dynamically populate the delegate list of a shared mailbox.
GETTING STARTED
In order to get started, you need to create one “Shadow Group” per mailbox who’s delegation properties you want to manage automatically. To make it as easy as possible, I’m using a prefix to identify the groups with the mailboxes, like Prefix-MailboxName. In my example below, the prefix is SM-. See the screenshot below for the correlation between them.

It could of course be possible to use another attribute on the groups to store the mailbox name, but I thought this was an easier approach.
RUNNING THE SCRIPT
After editing the credentials in the Connect-ExchangeOnline function, you simply run the script as below:
.\SharedMailboxViaGroups.ps1 -Prefix 'SM-'

As seen in the screenshot above it will process adds and removals of permissions for all mailboxes/groups in scope. Please note that both FullAccess and SendAs-permissions are added for each delegate.
SharedMailboxViaGroups.ps1
<#
.SYNOPSIS
The script will automatically assign mailbox and recipient permissions on shared mailboxes based on groups.
.EXAMPLE
.\SharedMailboxViaGroups.ps1 -Prefix 'SM-'
.PARAMETER Prefix
Prefix of the groups that will manage permissions on the shared mailboxes.
.NOTES
File Name: SharedMailboxViaGroups.ps1
Author : Johan Dahlbom, johan[at]dahlbom.eu
Blog : 365lab.net
The script are provided “AS IS” with no guarantees, no warranties, and they confer no rights.
Requires PowerShell Version 3.0!
#>
param (
[string]$Prefix = 'SM-'
)
function Connect-ExchangeOnline {
param(
[string]$Username = 'admin@tenant.onmicrosoft.com',
[string]$Password = 'password'
)
#Clean up existing PowerShell Sessions
Get-PSSession | Remove-PSSession
$CloudCred = New-Object –TypeName System.Management.Automation.PSCredential –ArgumentList $Username, (ConvertTo-SecureString $Password -AsPlainText -Force)
#Connect to Exchange Online
$Session = New-PSSession –ConfigurationName Microsoft.Exchange -ConnectionUri https://outlook.office365.com/powershell-liveid/ -Credential $CloudCred -Authentication Basic -AllowRedirection
$Commands = @("Add-MailboxPermission","Add-RecipientPermission","Remove-RecipientPermission","Remove-MailboxPermission","Get-MailboxPermission","Get-User","Get-DistributionGroupMember","Get-DistributionGroup","Get-Mailbox")
Import-PSSession -Session $Session -Prefix "Cloud" -DisableNameChecking:$true -AllowClobber:$true -CommandName $Commands | Out-Null
}
function Add-JDMailboxPermission {
param(
[string]$Identity,
[string]$SharedMailboxName
)
try {
Add-CloudMailboxPermission -Identity $SharedMailboxName -User $Identity -AccessRights FullAccess -ErrorAction stop | Out-Null
Add-CloudRecipientPermission -Identity $SharedMailboxName -Trustee $Identity -AccessRights SendAs -Confirm:$False -ErrorAction stop | Out-Null
Write-Output "INFO: Successfully added $Identity to $SharedMailboxName"
} catch {
Write-Warning "Cannot add $Identity to $SharedMailboxName`r`n$_"
}
}
function Remove-JDMailboxPermission {
param(
[string]$Identity,
[string]$SharedMailboxName
)
try {
Remove-CloudMailboxPermission -Identity $SharedMailboxName -User $Identity -AccessRights FullAccess -Confirm:$False -ErrorAction stop -WarningAction ignore | Out-Null
Remove-CloudRecipientPermission -Identity $SharedMailboxName -Trustee $Identity -AccessRights SendAs -Confirm:$False -ErrorAction stop -WarningAction ignore | Out-Null
Write-Output "INFO: Successfully removed $Identity from $SharedMailboxName"
} catch {
Write-Warning "Cannot remove $Identity from $SharedMailboxName`r`n$_"
}
}
function Sync-EXOResourceGroup {
[CmdletBinding(SupportsShouldProcess=$true)]
param(
[string]$Prefix = 'SM-'
)
#Get All groups to process mailboxes for
$MasterGroups = Get-CloudDistributionGroup -ResultSize Unlimited -Identity "$Prefix*"
foreach ($Group in $MasterGroups) {
#Remove prefix to get the mailbox name
$MbxName = $Group.Name.Replace("$Prefix",'')
$SharedMailboxName = (Get-CloudMailbox -Identity $MbxName -ErrorAction ignore -WarningAction ignore).WindowsLiveID
if ($SharedMailboxName) {
Write-Verbose -Message "Processing group $($Group.Name) and mailbox $SharedMailboxName"
#Get all users with explicit permissions on the mailbox
$SharedMailboxDelegates = Get-CloudMailboxPermission -Identity $SharedMailboxName -ErrorAction Stop -ResultSize Unlimited | Where-Object {$_.IsInherited -eq $false -and $_.User -ne "NT AUTHORITY\SELF" -and $_.User -notmatch 'S-\d-\d-\d+-\d+-\d+-\d+-\w+' -and $_.User -notlike "$Prefix*"} | Select-Object @{Name="User";Expression={(Get-CloudUser -identity $_.User).WindowsLiveID }}
#Get all group members
$SharedMailboxMembers = Get-CloudDistributionGroupMember -Identity $Group.Identity -ResultSize Unlimited
#Remove users if group is empty
if (-not($SharedMailboxMembers) -and $SharedMailboxDelegates) {
Write-Warning "The group $Group is empty, will remove explicit permissions from $SharedMailboxName"
foreach ($user in $SharedMailboxDelegates.User) {
Remove-JDMailboxPermission -Identity $user -SharedMailboxName $SharedMailboxName
}
#Add users if no permissions are present
} elseif (-not($SharedMailboxDelegates)) {
foreach ($user in $SharedMailboxMembers.WindowsLiveID) {
Add-JDMailboxPermission -Identity $user -SharedMailboxName $SharedMailboxName
}
#Process removals and adds
} else {
#Compare the group with the users that have actual access
$Users = Compare-Object -ReferenceObject $SharedMailboxDelegates.User -DifferenceObject $SharedMailboxMembers.WindowsLiveID
#Add users that are members of the group but do not have access to the shared mailbox
foreach ($user in ($users | Where-Object {$_.SideIndicator -eq "=>"})) {
Add-JDMailboxPermission -Identity $user.InputObject -SharedMailboxName $SharedMailboxName
}
#Remove users that have access to the shared mailbox but are not members of the group
foreach ($user in ($users | Where-Object {$_.SideIndicator -eq "<="})) {
Remove-JDMailboxPermission -Identity $user.InputObject -SharedMailboxName $SharedMailboxName
}
}
} else {
Write-Warning "Could not find the mailbox $MbxName"
}
}
}
#Connect to Exchange Online
Connect-ExchangeOnline
#Start Processing groups and mailboxes
Sync-EXOResourceGroup -Prefix $Prefix -Verbose
SUMMARY
A pretty simple solution on a very common problem in most environments where you have shared mailboxes. Let me know if you have feature requests or if something is not working as intended!
Enjoy!
/Johan






